-
Články
Top novinky
Reklama- Vzdělávání
- Časopisy
Nové číslo
- Témata
Top novinky
Reklama- Videa
- Podcasty
Nové podcasty
Reklama- Práce v oboru
Doporučené pozice
Reklama- Praktické
Top novinky
ReklamaDual-Use Research and Technological Diffusion: Reconsidering the Bioterrorism Threat Spectrum
article has not abstract
Published in the journal: . PLoS Pathog 7(1): e32767. doi:10.1371/journal.ppat.1001253
Category: Opinion
doi: https://doi.org/10.1371/journal.ppat.1001253Summary
article has not abstract
The global security community continues to view a potential bioterrorist event with concern. Kofi Annan, former Secretary General of the United Nations, stated “the most important under-addressed threat relating to terrorism…is that of terrorists using a biological weapon” [1]. The European Commission believes that biological weapons “may have particular attractions for terrorists” [2]. The United States Commission on the Prevention of Weapons of Mass Destruction Proliferation and Terrorism believes it is very likely that a weapon of mass destruction will be used in a terrorist attack by the end of 2013, and that an attack with a biological weapon is more likely than one with a nuclear weapon [3].
There is good reason for concern. Infectious diseases elicit instinctive fears that some terrorist organizations appear to have the intent to exploit [4]. The 2001 anthrax attacks in the United States, believed to have been caused by a single actor [5], were a keen reminder of the ability of bioterrorism to cause death and societal disruption. Such concerns have been linked to the rapid progress in life science research. The most advanced techniques 20 years ago are today routine (and some, like DNA synthesis, are also much cheaper [6]), while new fields, notably synthetic biology [7], [8], have opened frontiers previously inconceivable. Furthermore, expertise in life science research is globally dispersed, and methodologies for synthesizing and/or altering the virulence of pathogens in the laboratory have already been published in high-profile scientific journals. Activities that have garnered substantial attention include chemically synthesizing the poliovirus [9] and the ΦX174 bacteriophage [10], demonstrating the importance of a variola virus gene for its virulence [11], and reconstituting the 1918 influenza virus [12]. Each has been classified as dual use research of concern (DURC), which is defined by the US National Science Advisory Board for Biosecurity (NSABB) as “research that, based on current understanding, can be reasonably anticipated to provide knowledge, products, or technologies that could be directly misapplied by others” [13].
DURC creates a tension between freedom of research and national security [14]–[17]. As security communities have pushed for tighter oversight of research, scientific communities have been quick to grasp that certain biosecurity regulations, such as export controls [18] or visa controls for foreign scientists [19], run the risk of being inadvertently disruptive [20]–[24]. Members of the US NSABB have even argued that the inhibition of life science research could be considered a threat to national security and public health in and of itself [25]. Yet as concerns the rationale for biosecurity controls, the scientific community has been generally muted. Although this may be related to the secrecy surrounding intelligence about terrorist organizations, classified snippets of information should not have priority over expert technical input. Ceding the debate to the security community could lead to inaccurate threat assessments and the adoption of inappropriate biosecurity control measures.
The European Centre for Disease Prevention and Control (ECDC) was established in 2005 with the mandate to strengthen Europe's defenses against infectious diseases through developing European Union–wide surveillance networks and early warning systems, coordinating scientific studies, and identifying emerging health threats [26]. As a part of ECDC efforts to evaluate potential bioterrorism threats, we reviewed 27 assessments (published between 1997 and 2008) that address the links between life science research and bioterrorism with the objective of identifying DURC relevant for public health (Text S1). The focus of the review was limited to the application of DURC by terrorist organizations and it did not consider state-sponsored biological weapons programs.
The 27 assessments were selected based upon a literature review and interviews with a panel of international experts. Collectively, the 27 assessments explicitly cite a wide range of DURC activities. Based upon these, we conducted a threat assessment during an expert workshop. The purpose of this threat assessment was to identify those DURC activities that would be the most easily deployed by bioterrorists. The key parameters for this assessment were the level of expertise required for conducting any given DURC activity and the level of equipment required to conduct the work. In the threat assessment, an estimated threat level was calculated for each DURC activity by giving a score ranging from 1 (high threshold) to 3 (low threshold) for both parameters, and then multiplying these scores to yield the final threat, which could be 1, 2, 3, 4, 6, or 9. Higher scores indicate a higher likelihood of success if they were to be undertaken by bioterrorists (Text S1).
The overall ranking provides an indication of the threat spectrum related to the ability of bioterrorists to exploit life science research (Table 1), and it suggests that “low tech” activities may be especially attractive to bioterrorists. This opposes the tendency of biosecurity discussions to be rather more focused on “high tech” research: typically, the potential negative consequences of research falling into the wrong hands are accentuated while the likelihood of this occurring is inadequately considered. Is the availability of material, methodologies, and high-level expertise, none of which should be taken for granted, even adequate for the development of a sophisticated bioweapon? Technology is much more than the sum of its material and informational aspects. Social contingencies and tacit knowledge, serendipity and unpredictability, institutional memory, and many other factors are essential to the successful design and deployment of any given technology, including (if not especially) biological weapons [27], [28]. Interviews with the Wimmer group about the poliovirus synthesis [9], for example, highlight that replicating the experiment is a very challenging and time-consuming procedure even for virologists familiar with the experimental system [29]. It is not obvious that extrapolating the methods from this work for other purposes—or to another laboratory—would have been successful. The challenge is surely even greater when resource, time, or other constraints (such as the need to be clandestine) are involved.
Tab. 1. Threat assessment for research areas of concern. 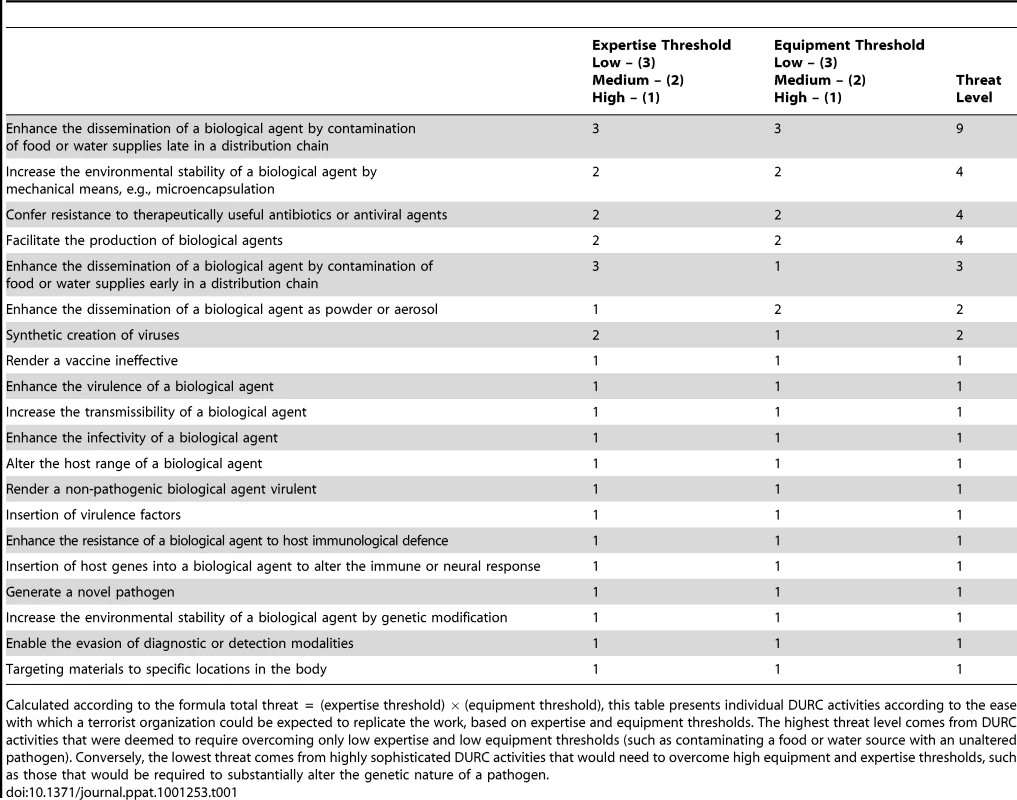
Calculated according to the formula total threat = (expertise threshold) × (equipment threshold), this table presents individual DURC activities according to the ease with which a terrorist organization could be expected to replicate the work, based on expertise and equipment thresholds. The highest threat level comes from DURC activities that were deemed to require overcoming only low expertise and low equipment thresholds (such as contaminating a food or water source with an unaltered pathogen). Conversely, the lowest threat comes from highly sophisticated DURC activities that would need to overcome high equipment and expertise thresholds, such as those that would be required to substantially alter the genetic nature of a pathogen. The recent history of bioterrorism also suggests that more attention should be allotted to low tech threats [30]. An extensive review of biocrimes in the 20th century argued that although bioterrorists might acquire some capabilities, there is “reason to doubt the ease with which such groups could cause mass casualties” [31]. Aum Shinrikyo, for example, was not successful in procuring, producing, or dispersing anthrax and botulinum toxin in the 1990s, while Al Qaeda is believed to have failed to obtain and work with pathogens by the early 2000s [32], and this likely remains the case. In comparison, the contamination of food and water, and direct injection/application of a pathogen, all have much lower technical hurdles and might be expected to be rather more successfully deployed [31]. The best-known example is the contamination of salad bars with Salmonella by the Rajneeshee cult in 1984, which led to roughly 751 illnesses and 45 hospitalizations [33]. It remains the only known incident in which a terrorist organization, rather than an individual, deployed a biological agent in the US [31].
We do not suggest that high tech bioterrorism threats do not exist—rather, that their likelihoods should be re-evaluated. Biosecurity policy discussions could gain more nuance and credibility by adopting more sophisticated notions about the challenges inherent in conducting and replicating advanced research. The life sciences community has an obvious self-interest in this, and might best achieve it by emphasizing the oft-unacknowledged factors inherent to successful high tech research, including those related to social contingencies and tacit knowledge. Thus far, when life scientists have entered the fray, they have tended to reinforce the “high-tech” perspective, even if their objectives have been to argue against strict biosecurity controls and/or to encourage the life sciences to engage in debates about the risks and benefits of its research [34]–[36].
Many agree about the importance of threat mitigation measures that prepare for the eventuality of a bioterrorism attack, irrespective of its source [37], [38]. Examples include encouraging the development of diagnostics, vaccines, and therapeutics, as well as empowering public health agencies to strengthen defenses against communicable diseases. Such approaches have the additional advantage that they take the broadest possible view of the threat spectrum by also preparing for attacks by the most successful “bioterrorists” of all, nature and globalization, which have led to the emergence of numerous new communicable diseases in recent years [39]–[41]. A focus on strengthening global health security has been put forward by the Obama administration [42] and the European Commission [38], and has also gained prominence in fora such as the Biological and Toxin Weapons Convention [43]. Public health, too, is dual use: it can be leveraged to counter natural and intentional disease outbreaks.
Supporting Information
Zdroje
1. United Nations 2006 Uniting against terrorism: recommendations for a global counter-terrorism strategy, report of the Secretary-General. United Nations Report A/60/825. Geneva United Nations Available: http://www.un.org/unitingagainstterrorism/contents.htm. Accessed 10 December 2010
2. The Council of the European Union 2003 European Union strategy against the proliferation of weapons of mass destruction. Document no. 15708/3. Brussels: Council of the European Union. Available: http://register.consilium.europa.eu/pdf/en/03/st15/st15708.en03.pdf. Accessed 10 December 2010
3. United States Commission on the Prevention of Weapons of Mass Destruction Proliferation and Terrorism 2008 World at risk: the report of the Commission on the Prevention of WMD Proliferation and Terrorism. New York Vintage Books 160
4. Kurth CroninA
2003 Terrorist motivations for chemical and biological weapons use: placing the threat in context. Report for Congress. Available: http://www.fas.org/irp/crs/RL31831.pdf. Accessed 10 December 2010
5. BhattacharjeeY
2009 The danger within. Science 323 1282 1283
6. Service RF 2006 The race for the $1000 genome. Science 311 1544 1546
7. GarfinkelMS
WendyD
EpsteinGL
FriedmanRM
2007 Synthetic genomics: options for governance. Biosecur Bioterror 5 359 362
8. GibsonDG
GlassJI
LartigueC
NoskovVN
ChuangR-Y
2010 Creation of a bacterial cell controlled by a chemically synthesized genome. Science 329 52 56
9. CelloJ
PaulAN
WimmerE
2002 Chemical synthesis of poliovirus cDNA: Generation of infective virus in the absence of a natural template. Science 297 1016 1018
10. SmithHO
HutchinsonCA3rd
PfannkochC
VenterJC
2003 Generating a synthetic genome by whole genome assembly: phiX174 bacteriophage from synthetic oligonucleotides. Proc Natl Aca Sci USA 100 15440 15445
11. RosengardAM
LiuY
NieZ
JimenezR
2002 Variola virus immune evasion design: Expression of a highly efficient inhibitor of human complement. Proc Natl Acad Sci USA 99 8808 8813
12. TaubenbergerJK
ReidAH
LourensRM
WangR
JinG
2005 Characterization of the 1918 influenza virus polymerase genes. Nature 437 889 893
13. NSABB 2010 NSABB frequently asked questions. What is “dual use research” and “dual use research of concern”? Available: http://oba.od.nih.gov/biosecurity/nsabb_faq.html#NSABB_FAQ001. Accessed 10 December 2010
14. National Research Council 2004 Biotechnological research in an age of terrorism. Washington (D.C.) National Academies Press
15. KennedyD
2008 Science and security, again. Science 321 1019
16. SukJ
2008 Containing biological weapons, constraining biological research? Sci Pub Pol 35 2 5
17. SukJ
SemenzaJC
The Praeger handbook of environmental health 2011 Biodefence and bioterrorism.
FriisRH
Westport (Connecticut): Praeger Publishers In press
18. The Australia Group 2010 Australia Group Common control lists. Available: http://www.australiagroup.net/en/controllists.html. Accessed 10 December 2010
19. BhattacharjeeY
2009 U.S. promises to reduce delays in granting visas for scientists. Science 324 1377
20. GaudiosoJ
SalernoRM
2004 Biosecurity and research: minimizing adverse impacts. Science 304 687
21. AtlasRM
2002 National security and the biological research community. Science 298 753 754
22. American Association for the Advancement of Science 2010 Science and security in the post-9/11 environment. Foreign students and scholars. Available: http://www.aaas.org/spp/post911/visas/. Accessed 10 December 2010
23. RelmanDA
ChoffnesE
LemonSM
2006 In search of biosecurity. Science 311 1835
24. Beatrice-DiasM
Reyes-GonzalezL
VelosoFM
CasmanEA
2010 Effects of the USA PATRIOT Act and the 2002 Bioterrorism Preparedness Act on select agent research in the United States. Proc Natl Acad U S A 107 9556 9561
25. FranzDR
EhrlichSA
CasadevallA
ImperialeMJ
KeimPS
2009 The “nuclearization” of biology is a threat to health and security. Biosecur Bioterror 7 243 244
26. European Centre for Disease Prevention and Control 2010 About us: our mission. Available: http://ecdc.europa.eu/en/About_us/Default.aspx. Accessed 10 December 2010
27. NightingaleP
2004 Technological capabilities, invisible infrastructure and the un-social construction of predictability: the overlooked fixed costs of useful research. Res Policy 33 1259 1284
28. MacKenzieD
SpinardiG
1996 Tacit knowledge and the uninvention of nuclear weapons.
MacKenzieD
Knowing machines: essays on technological change Cambridge (Massachusetts) MIT Press
29. VogelK
2008 Framing biosecurity: An alternative to the Biotech Revolution Model? Sci Pub Pol 35 45 54
30. TuckerJB
SandsA
1999 An unlikely threat. B Atom Sci 55 46 52
31. CarusWS
2001 Bioterrorism and biocrimes: the illicit use of biological agents since 1900. February 2001 revision. Washington (D.C.) Center for Counterproliferation Research, National Defense University Available: http://www.fas.org/irp/threat/cbw/carus.pdf. Accessed 10 December 2010
32. LeitenbergM
2005 Assessing the biological weapons and bioterrorism threat. Carlisle (Pennsylvania) Strategic Studies Institute, U.S. Army War College Available: http://www.cissm.umd.edu/papers/files/assessing_bw_threat.pdf. Accessed 10 December 2010
33. TörökTJ
TauxeRV
WiseRP
LivengoodJR
SokolowR
1997 A large community outbreak of salmonellosis caused by intentional contamination of restaurant salad bars. JAMA 278 389 395
34. CarlsonR
2003 The pace and proliferation of biological technologies. Biosecur Bioterror 1 203 214
35. RelmanDA
2010 The biological century: coming to terms with risk in the life sciences. Nat Immunol 11 275 278
36. ChoMK
RelmanDA
2010 Synthetic “life,” ethics, national security, and public discourse. Science 329 38 39
37. O'TooleT
InglesbyT
2009 Strategic priorities for U.S. biosecurity. Biosecur Bioterror 7 25 28
38. Commission of the European Union 2007 Green paper on bio-preparedness. Brussels: European Commission. Available: http://eur-lex.europa.eu/LexUriServ/LexUriServ.do?uri=COM:2007 : 0399:FIN:EN:PDF. Accessed 10 December 2010
39. Institute of Medicine 2003 Microbial threats to health: emergence, detection, and response. Washington (D.C.) National Academy Press
40. WoolhouseMEJ
Gowtage-SequeriaS
2005 Host range and emerging and reemerging pathogens. EID 11 1842 1847
41. JonesKE
PatelNG
LevyMA
StoreygardA
BalkJ
2008 Global trends in emerging infectious diseases. Nature 451 990 994
42. The White House & US National Security Council 2009 National strategy for countering biological threats. Available: http://www.whitehouse.gov/sites/default/files/National_Strategy_for_Countering_BioThreats.pdf. Accessed 10 December 2010
43. United Nations Office at Geneva 2009 Report of the meeting of the states parties. Available: http://www.unog.ch/80256EDD006B8954/%28httpAssets%29/7C047AF3CA49AE1CC1257689005E0420/file/Draft-BWC_MSP_2009_Advance-Report.pdf. Accessed 10 December 2010
Štítky
Hygiena a epidemiologie Infekční lékařství Laboratoř
Článek vyšel v časopisePLOS Pathogens
Nejčtenější tento týden
2011 Číslo 1- Farmakovigilanční studie perorálních antivirotik indikovaných v léčbě COVID-19
- Jak souvisí postcovidový syndrom s poškozením mozku?
- Měli bychom postcovidový syndrom léčit antidepresivy?
- 10 bodů k očkování proti COVID-19: stanovisko České společnosti alergologie a klinické imunologie ČLS JEP
-
Všechny články tohoto čísla
- Salivary Gland NK Cells Are Phenotypically and Functionally Unique
- Genetic Epidemiology of Tuberculosis Susceptibility: Impact of Study Design
- Early Target Cells of Measles Virus after Aerosol Infection of Non-Human Primates
- Multiple Plant Surface Signals are Sensed by Different Mechanisms in the Rice Blast Fungus for Appressorium Formation
- Biofilm Development on by Is Facilitated by Quorum Sensing-Dependent Repression of Type III Secretion
- Distinct Patterns of IFITM-Mediated Restriction of Filoviruses, SARS Coronavirus, and Influenza A Virus
- Molecular Basis of Increased Serum Resistance among Pulmonary Isolates of Non-typeable
- A Helminth Immunomodulator Exploits Host Signaling Events to Regulate Cytokine Production in Macrophages
- HCMV Spread and Cell Tropism are Determined by Distinct Virus Populations
- Characteristics of the Earliest Cross-Neutralizing Antibody Response to HIV-1
- Induction of a Peptide with Activity against a Broad Spectrum of Pathogens in the Salivary Gland, following Infection with Dengue Virus
- Structural Basis for the Recognition of Cellular mRNA Export Factor REF by Herpes Viral Proteins HSV-1 ICP27 and HVS ORF57
- Identification and Characterization of the Host Protein DNAJC14 as a Broadly Active Flavivirus Replication Modulator
- Dual-Use Research and Technological Diffusion: Reconsidering the Bioterrorism Threat Spectrum
- Pathogenesis of the 1918 Pandemic Influenza Virus
- A Cardinal Role for Cathepsin D in Co-Ordinating the Host-Mediated Apoptosis of Macrophages and Killing of Pneumococci
- Critical Role of IRF-5 in the Development of T helper 1 responses to infection
- The Pel Polysaccharide Can Serve a Structural and Protective Role in the Biofilm Matrix of
- Selective C-Rel Activation via Malt1 Controls Anti-Fungal T-17 Immunity by Dectin-1 and Dectin-2
- Imaging Single Retrovirus Entry through Alternative Receptor Isoforms and Intermediates of Virus-Endosome Fusion
- Aerosols Transmit Prions to Immunocompetent and Immunodeficient Mice
- PLOS Pathogens
- Archiv čísel
- Aktuální číslo
- Informace o časopisu
Nejčtenější v tomto čísle- Dual-Use Research and Technological Diffusion: Reconsidering the Bioterrorism Threat Spectrum
- Pathogenesis of the 1918 Pandemic Influenza Virus
- Critical Role of IRF-5 in the Development of T helper 1 responses to infection
- A Cardinal Role for Cathepsin D in Co-Ordinating the Host-Mediated Apoptosis of Macrophages and Killing of Pneumococci
Přihlášení#ADS_BOTTOM_SCRIPTS#Zapomenuté hesloZadejte e-mailovou adresu, se kterou jste vytvářel(a) účet, budou Vám na ni zaslány informace k nastavení nového hesla.
- Vzdělávání



